Six Reasons Why You Should Restart Your Mac Periodically
Long ago, before macOS was as stable as it is today, Mac users restarted their Macs regularly. Back then, Macs couldn’t sleep, either, so it was common for users to shut down at the end of the day and start up the next morning, effectively restarting daily.
With modern Macs using the barest trickle of power in sleep and both apps and macOS almost never crashing, many Mac users have gone to the opposite extreme, letting their Macs run for months between restarts. However, such an approach brings with it new problems, and as with so many things, there’s a happy medium.
Why are we banging this particular drum? As an off-the-cuff estimate, about a quarter of the problems reported to us can be solved by a restart. Really! Just click the Apple menu and choose Restart. As long as you save your work first or when prompted, nothing bad will happen.
Here are our top six reasons you should restart periodically:
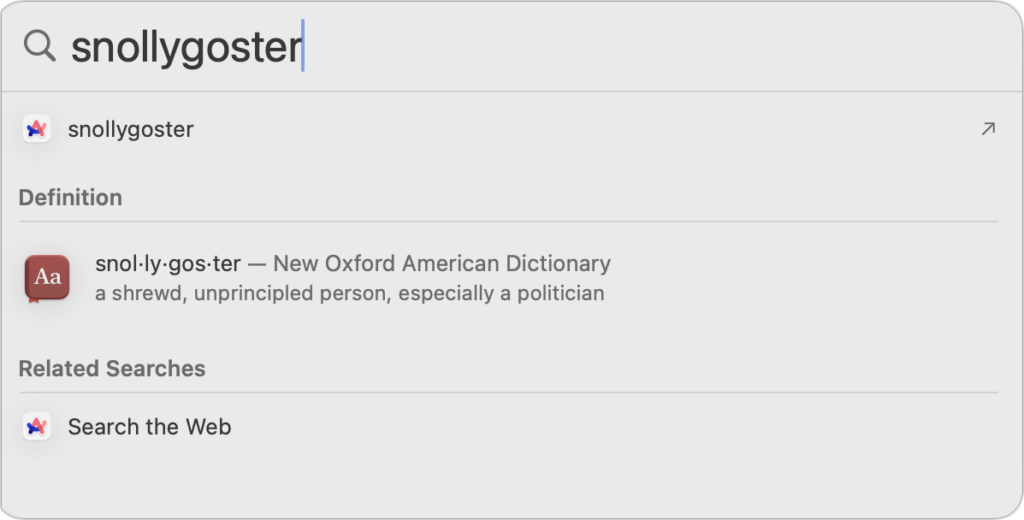
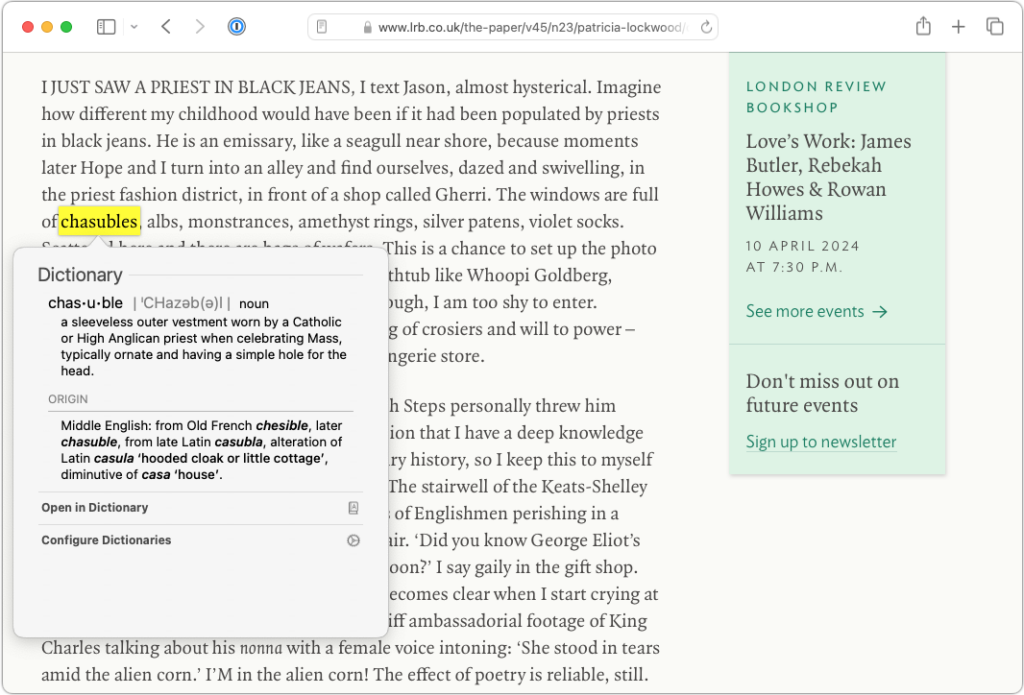
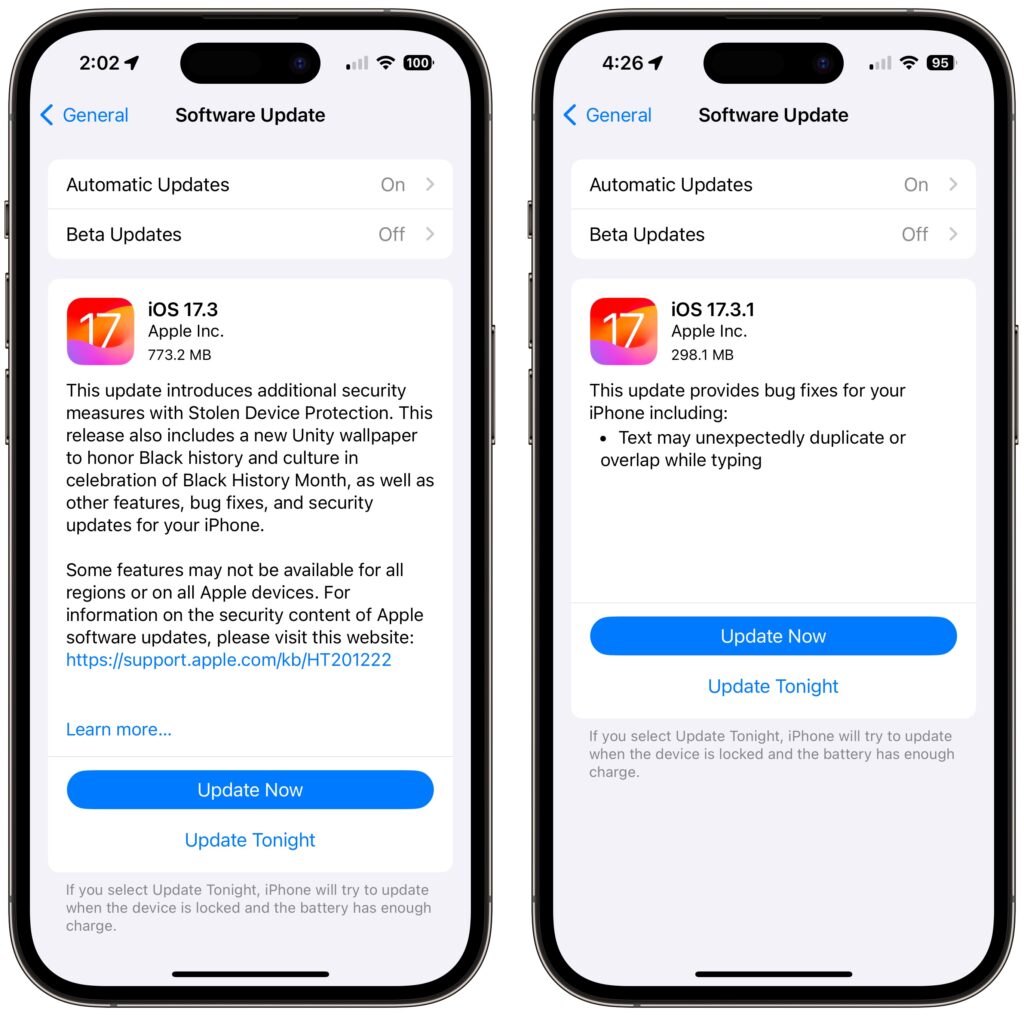
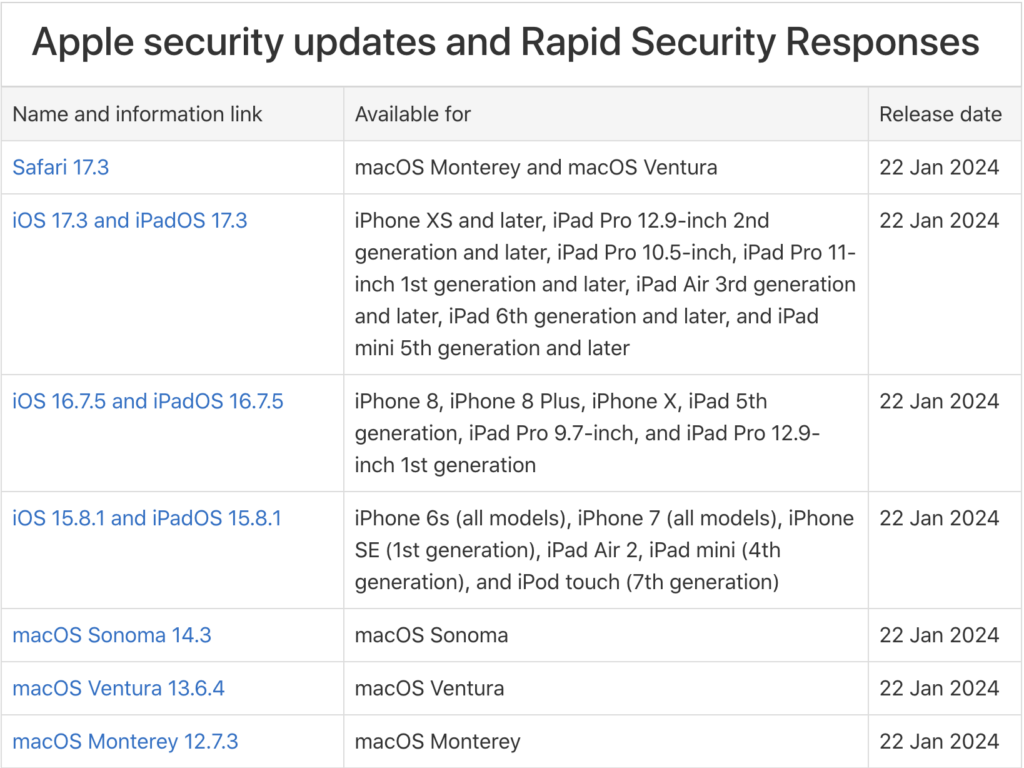
- Improved security: Restarting itself doesn’t generally improve security (although it could theoretically clear malicious code running in memory). However, installing macOS updates requires a restart, and we strongly recommend installing security-focused updates shortly after they’re released. If you resist installing updates because of the need to restart, you’re increasing your risk significantly.
- Resolve problems: Modern Macs may be more stable than ever, but things can still get funky. If apps are crashing, peripherals aren’t connecting, you’re seeing visual glitches, or anything else seems wrong, the first troubleshooting step is a restart.
- Better performance: We all have a feel for how long different tasks on our Macs take. If icons for launching apps bounce longer than usual, windows draw slowly, or you see the spinning pinwheel repeatedly, restart. Performance problems are often caused by a poorly coded app or out-of-control process causing your Mac to run out of physical memory and switch to slower virtual memory. Restarting clears such issues.
- Recover drive space: Another memory-related bonus of restarting is that it can free up drive space. When macOS starts to rely on virtual memory, it creates swap files that can consume gigabytes of space. Restart, and all that space is returned, at least until your app usage requires it again.
- Get updates: Most apps notify you of updates at launch, and some automatically download their updates but install them only when you quit. Either way, a restart results in all your apps quitting and relaunching, which ensures they either install or at least notify you of important updates.
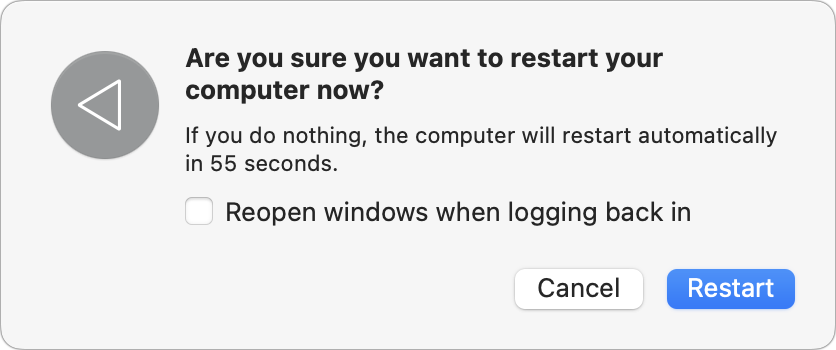
- Start fresh: Even if having 20 or more apps open isn’t affecting your Mac’s performance, a clean slate can help you focus on your work better. A simple restart quits everything and lets you start over with just those apps set to launch at login. For a completely fresh start, make sure to deselect “Reopen windows when logging back in” in the restart dialog. Of course, if you have a lot of documents open and need to return to them, leave that checkbox selected to pick up exactly where you left off.
There’s no set schedule on which you should restart, but if you use a Mac at work and like routines, it wouldn’t be problematic to restart on Friday evening as you wind down to leave for the weekend. That way, you’d return to a clean slate on Monday morning. It’s also totally fine to restart whenever it might be helpful.
Just don’t fear the restart—modern Macs, especially those with Apple silicon, restart quickly, and the benefits far outweigh the few minutes of downtime.
(Featured image based on an original by iStock.com/Armastas)