Here’s Why You Should Always Keep the Find My iPhone Feature Enabled
On the face of it, Apple’s Find My iPhone feature does what it says. If you lose your iPhone, you can identify its last known location by looking in the Find iPhone app or on the iCloud Web site, and you can make it play a sound. It’s great for tracking down a missing iPhone, whether you misplaced it in the house or left it behind at a restaurant.
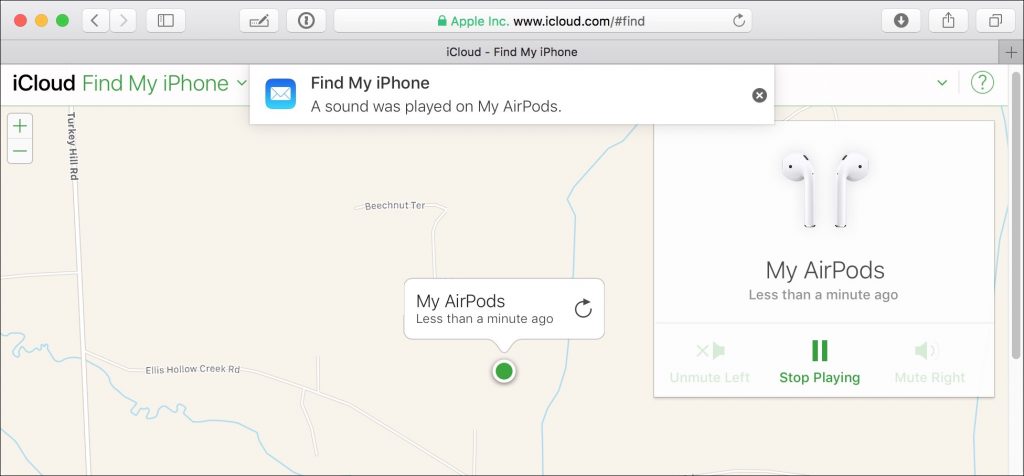
But Find My iPhone does much more! For starters, it works with nearly any Apple device. You can use it to locate a missing Mac, iPad, iPod touch, Apple Watch, and even AirPods. Find My iPhone also helps protect your data if a device is stolen. It even works with Family Sharing to locate devices owned by anyone in your family—a boon to any parent with a forgetful teenager.
You must turn on Find My iPhone before your device goes missing!
- In iOS, tap Settings > Your Name > iCloud > Find My iPhone and enable Find My iPhone. (On the iPad, it’s called Find My iPad.) Also on that screen, turn on Send Last Location. Finally, go back to the main level of Settings, tap Privacy > Location Services, and make sure Location Services is turned on.
- On the Mac, open System Preferences > iCloud and select the Find My Mac checkbox—if you see a Details button beside Find My Mac, click it and follow its instructions for setting necessary preferences.
Be sure to practice viewing where your devices are located and playing tones on them so you’ll know what to do if a device goes missing.
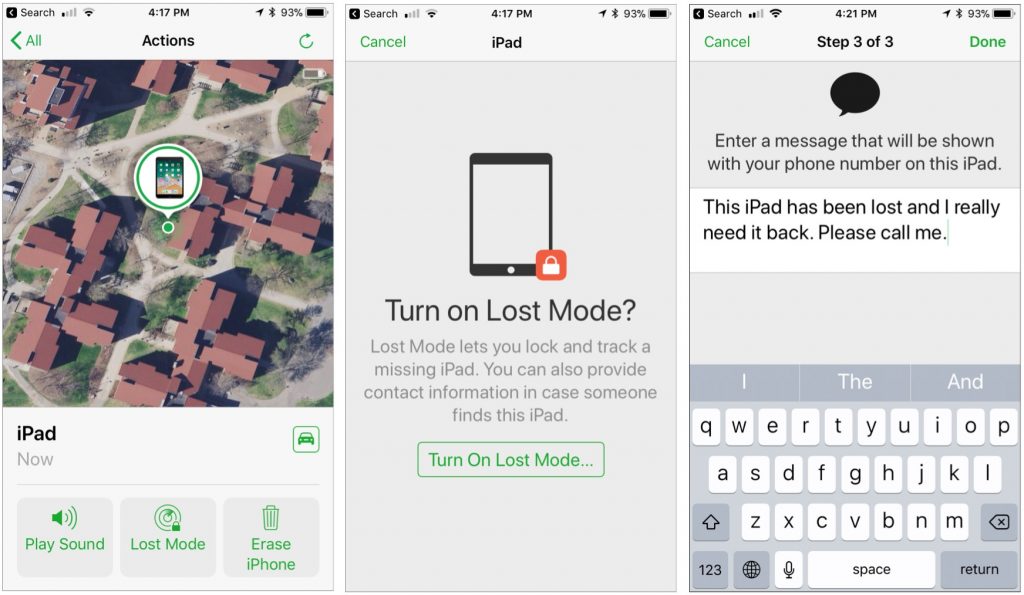
Find My iPhone has a few tricks up its sleeve for when you want a device to show a message or if you think it was stolen:
- Lost Mode: When invoking this mode for an iOS device or Apple Watch, you’ll be asked to enter a phone number where you can be reached and a message. After that, Lost Mode will kick in as soon as the device is awake and has an Internet connection. Anyone who tries to use the device will see your message along with a place to enter the device’s passcode. If you get it back, you can enter the passcode to dismiss the message and use it normally.
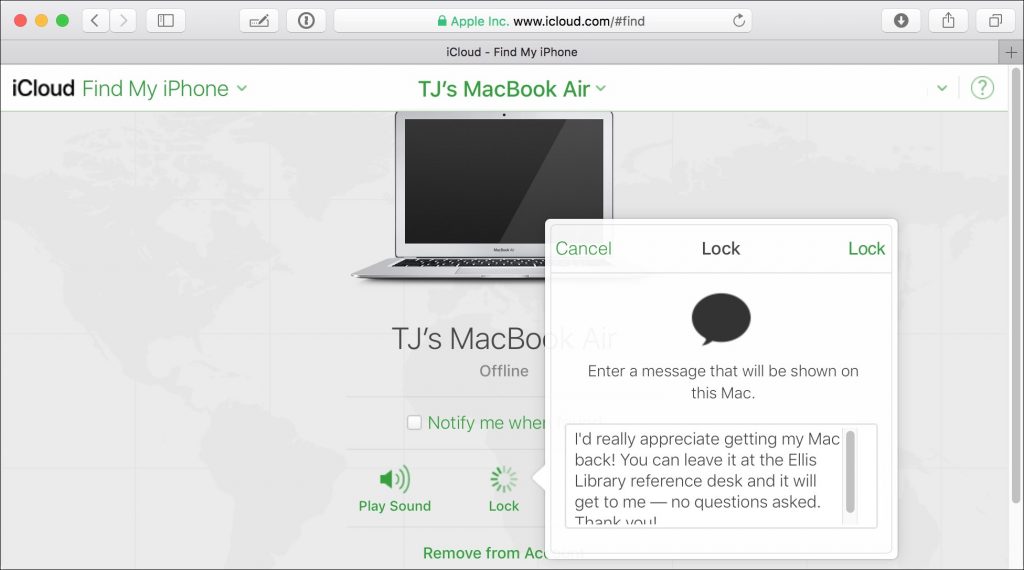
- Lock: Available only for the Mac, the Lock feature enables you to protect an entire Mac with a 4-digit custom passcode. You can also enter a message that will appear on the Lock screen. This is a good choice if you think you’ll get your Mac back but would prefer that nobody mess with it in the meantime. Note that if you lock a Mac, you can’t erase it, as discussed next, so lock it only if you think it can be recovered.
- Erase: Even if your device has an excellent passcode or password, you might worry that a thief will access your data. Fortunately, you can erase your device. Erasing a device makes it impossible for you to see its location in Find My iPhone, so it’s a last-ditch effort.
- Activation Lock: If the stolen device is an iOS device or an Apple Watch, when you turn on Find My iPhone, you also enable Activation Lock. This feature prevents someone who has your passcode but doesn’t know your Apple ID and password from turning off Find My iPhone, erasing the device, or setting it up for a new user. In other words, Activation Lock makes it so there’s little reason to steal an iOS device or Apple Watch, since the stolen device can’t ever be used by anyone else. If you get the device back, you can restore your backup—you do have a backup, right?
Find My iPhone works only while the device has power, so if you think you’ve mislaid a device, try locating it right away, before the battery runs out. But even if you are unable to retrieve a lost device, you can prevent others from accessing your data or taking over the device.











 The longer you use Siri and Dictation, the better they work, thanks to your devices transmitting data back to Apple for analysis. However, Apple creates a random identifier for your data rather than associating the information with your Apple ID, and if you reset Siri by turning it off and back on, you’ll get a new random identifier. Whenever possible, Apple keeps Siri functionality on your device, so if you search for a photo by location or get suggestions after a search, those results come from local data only.
The longer you use Siri and Dictation, the better they work, thanks to your devices transmitting data back to Apple for analysis. However, Apple creates a random identifier for your data rather than associating the information with your Apple ID, and if you reset Siri by turning it off and back on, you’ll get a new random identifier. Whenever possible, Apple keeps Siri functionality on your device, so if you search for a photo by location or get suggestions after a search, those results come from local data only. When you register your fingerprints with Touch ID or train Face ID to recognize your face, it’s reasonable to worry about that information being stored where attackers—or some government agency—could access it and use it for nefarious purposes. Apple was concerned about that too, so these systems don’t store images of your fingerprints or face, but instead mathematical signatures based on them. Those signatures are kept only locally, in the Secure Enclave security coprocessor that’s part of the CPU of the iPhone and iPad—and on Touch ID-equipped laptops—in such a way that the images can’t be reverse engineered from the signatures.
When you register your fingerprints with Touch ID or train Face ID to recognize your face, it’s reasonable to worry about that information being stored where attackers—or some government agency—could access it and use it for nefarious purposes. Apple was concerned about that too, so these systems don’t store images of your fingerprints or face, but instead mathematical signatures based on them. Those signatures are kept only locally, in the Secure Enclave security coprocessor that’s part of the CPU of the iPhone and iPad—and on Touch ID-equipped laptops—in such a way that the images can’t be reverse engineered from the signatures. People with medical conditions can be concerned about health information impacting health insurance bills or a potential employer’s hiring decision. To assuage that worry, Apple lets you choose what information ends up in Health app, and once it’s there, encrypts it whenever your iPhone is locked. Plus, any Health data that’s backed up to iCloud is encrypted both in transit and when it’s stored on Apple’s servers.
People with medical conditions can be concerned about health information impacting health insurance bills or a potential employer’s hiring decision. To assuage that worry, Apple lets you choose what information ends up in Health app, and once it’s there, encrypts it whenever your iPhone is locked. Plus, any Health data that’s backed up to iCloud is encrypted both in transit and when it’s stored on Apple’s servers. A linchpin in Apple’s approach to privacy is its control over the App Store. Since developers must submit apps to Apple for approval, Apple can enforce stringent guidelines that specify how apps can ask for access to your data (location, photos, contacts, etc.). This isn’t a blanket protection—for instance, if you allow a social media app <cough>Facebook<cough> to access your contacts and location, the company behind that app will get lots of data on your whereabouts and can even cross-reference that with the locations of everyone in your contact list who also uses the service.
A linchpin in Apple’s approach to privacy is its control over the App Store. Since developers must submit apps to Apple for approval, Apple can enforce stringent guidelines that specify how apps can ask for access to your data (location, photos, contacts, etc.). This isn’t a blanket protection—for instance, if you allow a social media app <cough>Facebook<cough> to access your contacts and location, the company behind that app will get lots of data on your whereabouts and can even cross-reference that with the locations of everyone in your contact list who also uses the service.